
See What's New in Global Security
Cisco Security Intelligence Operations announces the Cisco 2009 Annual Security Report. The updated report includes information about 2009 global threats and trends, as well as security recommendations for 2010.
Managing and securing today's distributed and agile network is increasingly challenging, with cloud computing and sharing of data threatening security norms. Online criminals are continuing to exploit users trust in consumer applications and devices, increasing the risk to organizations and employees.
Report Highlights
•Online criminals have taken advantage of the large social media following, exploiting users' willingness to respond to messages that are supposedly from people they know and trust.
•Politically-motivated threats are increasing, while governments are teaming up and promoting online security.
•Up to 90 percent of spam is untargeted. That includes spam delivered by botnets that floods inboxes with messages from supposed banks, educational institutions, and service providers.
•More than 80 percent of the web can be classified as “uncategorized” or “unknown”, making it challenging for traditional URL filtering technology.
•The new Cisco Cybercrime Return on Investment Matrix tracks the performance of the underground online criminal marketplace, helping organizations understand the latest targets.
Key Findings
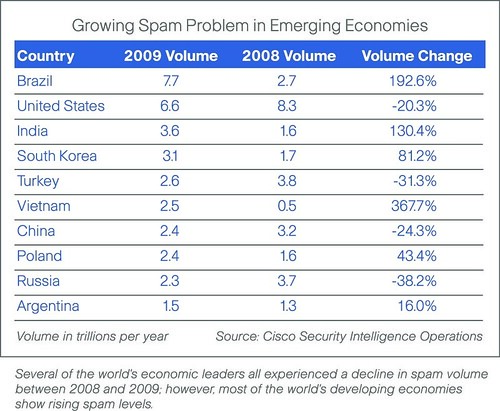
• Spam: Social media may be where cybercriminals troll for new victims. However, spam is still a tried-and-true means for tricking people into downloading malware and persuading them to buy, for example, fake pharmaceuticals. The Annual Security Report estimates that in 2010, spam volume will likely rise 30 to 40 percent worldwide over 2009 levels. However, Cisco's own SensorBase data shows that while the U.S. and other economic leader countries (such as those within the European Union) begin to shut down spam zombies in their own countries, the rollout of broadband in developing economies (including India and Vietnam) have made them an increasing source of spam. In fact, the U.S. was toppled as the No. 1 spam sender. In 2009, that distinction went to Brazil.
• Cloud Computing: While 10 years ago it would have been unthinkable for businesses to keep sensitive data outside the corporate firewall, today, with the advent of cloud computing and hosted applications, doing so is increasingly common. Many users are so trusting of cloud computing that they do minimal due diligence on who's hosting their sensitive data, and how secure the data is. The Annual Security Report recommends that organizations looking to use externalized services ask providers to explain their data security measures thoroughly.
• Cisco Cybercrime Return on Investment (CROI) Matrix:This year's Annual Security Report marks the debut of the Cisco CROI Matrix, based on the Boston Consulting Group's well-known "Growth-Share Matrix." The CROI Matrix analyzes which types of cybercrime will be the "winners" and "losers" in 2010. Based on performance in 2009, the matrix predicts that massive banking Trojan Zeus and other lucrative and easy-to-deploy Web exploits will be more prevalent in 2010. Scareware, spyware, click fraud, advance-fee fraud and pharma spam will continue to be cash cows. The "wait-and-see" moneymakers include social networking exploits, like the Koobface worm, that are only now starting to make their mark.
• Cisco Global ARMS Race Index: In an effort to track the overall level of compromised resources worldwide, Cisco has developed a Global Adversary Resource Market Share (ARMS) Race Index. Over time, the index will give a better picture of the online criminal community's rate of success at compromising enterprise and individual activity. In 2009, the index rates the level of resources under adversarial control at 7.2, indicating that between 5 and 10 percent of personal computers are compromised.
Download
No hay comentarios:
Publicar un comentario