By Michael Messner
If you have enabled IPv6 on your network without
considering basic security issues, you might have opened up a hole for
attackers. In this article, we demonstrate a successful attack on a
server via IPv6 and explain how the popular security tools handle IPv6.
Although the “next generation” IPv6 Internet protocol can already
look back on more than 10 years of history, many companies are only now
starting to migrate to the new version. Some experts have already begun
to point out that IPv6 security has some unexpected complications for
admins who are accustomed to IPv4 networks. One such under-mentioned
problem is the need to lock down or turn off IPv6 services that might be
running on an IPv4 or a dual IPv4/IPv6 network. Some modern systems
enable IPv6 by default. Even if your network is primarily focused on
IPv4, it is a good idea to pay some special attention to IPv6 in your
pen testing. You might discover that your systems are vulnerable to
exploits in IPv6 that aren’t available (or don’t appear) through
conventional IPv4 pen tests.
In this article, I take a brief look at some IPv6 testing modules available through the Metasploit framework.
In this case, I set up a scenario for my tests within our security
testing lab; however, these techniques will help you search out other
exploits hidden on your transitional IPv4/IPv6 mixed network.
Looking Around
All
recent operating systems are capable of using the IPv6 protocol and
often enable it by default. On Linux, you can verify that IPv6 is
enabled with a simple test using ifconfig or ip (Listing 1). The output for the interface configuration should contain at least one inet6
entry. If an IPv6-enabled router exists on the internal network, the
system might already be configured with a global address in addition to
the link-local address.
Listing 1: ifconfig and ip
01 root@bt:~# ifconfig -a 02 eth0 Link encap:Ethernet HWaddr 00:0c:29:7c:e7:6a 03 inet addr:192.168.11.138 Bcast:192.168.11.255 Mask:255.255.255.0 04 inet6 addr: fe80::20c:29ff:fe7c:e76a/64 Scope:Link 05 [...] 06 root@bt:~# ip -6 addr 07 [...] 08 1: lo:mtu 16436 09 inet6 ::1/128 scope host 10 valid_lft forever preferred_lft forever 11 [...] 12 2: eth0: mtu 1500 qlen 1000 13 inet6 fe80::20c:29ff:fecf:6aba/64 scope link 14 valid_lft forever preferred_lft forever
The presence of an inet6
entry doesn’t automatically mean the computer is accessible from
external addresses. The scope link in line 4 of Listing 1 means that the
address is only used on the local subnet; it is not routed beyond
router or network boundaries. Listing 2 shows what the configuration
looks like when the network contains an IPv6-capable router.
Listing 2: Global Scope
inet6 addr: 2001:4dd0:fd42:3:20c:29ff:fe7c:e76a/64 Scope:Global** [...] inet6 addr: fd44:2011:1021:0:20c:29ff:fe7c:e76a/64 Scope:Global** [...] inet6 addr: fe80::20c:29ff:fe7c:e76a/64 Scope:Link**
A simple test of the IPv6 functions is to ping6 to the loopback interface:
root@bt:~# ping6 ::1 -c1 PING ::1(::1) 56 data bytes 64 bytes from ::1: icmp_seq=1 ttl=255 time=0.052 ms --- ::1 ping statistics --- 1 packets transmitted, 1 received, 0% packet loss, time 0ms rtt min/avg/max/mdev = 0.052/0.052/0.052/0.000 ms
Just as with IPv4, you can ping the broadcast address (in IPv6, this is FF02::1;
all the systems on the local network respond to this). Consequently,
the following simple command already offers an initial overview of the
local network:
root@bt:~# ping6 ff02::1%2 | cut -d\ -f4 fe80::20c:29ff:fecf:6aba: fe80::20c:29ff:fe5c:e4b6: fe80::20c:29ff:fef5:b6b0: fe80::20c:29ff:fe01:95e3: [...]
If you sort the output, remove duplicate entries with uniq, and redirect the results to a text file, you already have a good basis for further analysis.
IPv6 and Metasploit
Many
well-known analysis tools are now ready to work with IPv6 systems. You
can use Nessus, Nmap, and Wireshark to analyze IPv6-capable networks.
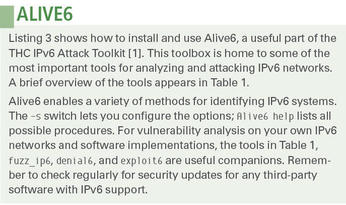
Alive6, for instance, offers several tools for analyzing possible IPv6
vulnerabilities (see the sidebar titled “Alive6”). In this article,
however, I will focus on Metasploit.
Fuente: www.linux-magazine.com
No hay comentarios:
Publicar un comentario